Installing and using PGP on Mac OS X
This is a work in progress
Under Mac OS X, PGP is already installed in the form of the free software GNU Privacy Guard (GPG). You can check out the program and the version you have from the Terminal application (Applications->Utilities->Terminal). For example:
Last login: Fri Mar 5 08:11:22 on console fantasia:~ miguelr$ gpg --version gpg (GnuPG) 1.4.8 Copyright (C) 2007 Free Software Foundation, Inc. License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html> This is free software: you are free to change and redistribute it. There is NO WARRANTY, to the extent permitted by law.
Now everything will work fine without the need to install anything else, you can encrypt messages and files already with this program installed. However, there is a rather nice graphical front end to GPG, called the GNU Privacy Guard, the latest version of which is 1.4.9. Download and install this:
http://prdownloads.sourceforge.net/macgpg/GnuPG1.4.9.dmg?download
You download this and it should create a virtual disc automatically and open it to show the following window (if it doesn't do this, double-click the file that was downloaded):
Double click the icon GnuPG for Mac OS X 1.4.9.mpkg (or similar, perhaps you downloaded a more recent version).
At each stage, click Continue and also Agree to the licence agreement when asked about it. When you get there, click the Install button. Then you'll be prompted for your password, type it in and the software should install for you and display a warning telling you it did so. At this point click the Close button.
Creating a new key for yourself
Having installed Mac Gnu Privacy Guard, you'll spot a number of new things installed on your computer.
Use the Finder to go to Applications -> Utilities and start the programme GPG Keychain Access:
The Terminal method
fantasia:~ miguelr$ gpg --gen-key
gpg (GnuPG) 1.4.9; Copyright (C) 2008 Free Software Foundation, Inc.
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law.
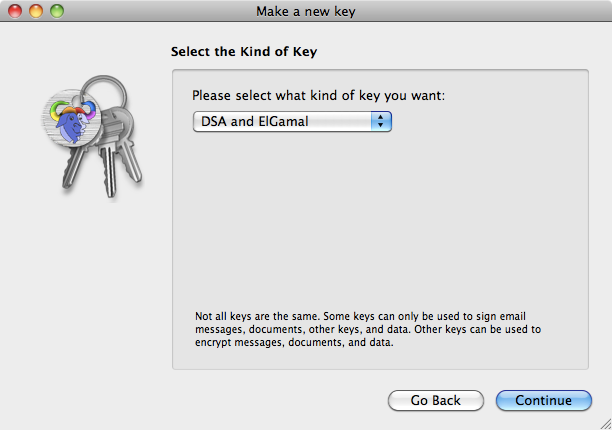
Please select what kind of key you want:
(1) DSA and Elgamal (default)
(2) DSA (sign only)
(5) RSA (sign only)
Your selection? 1
DSA keypair will have 1024 bits.
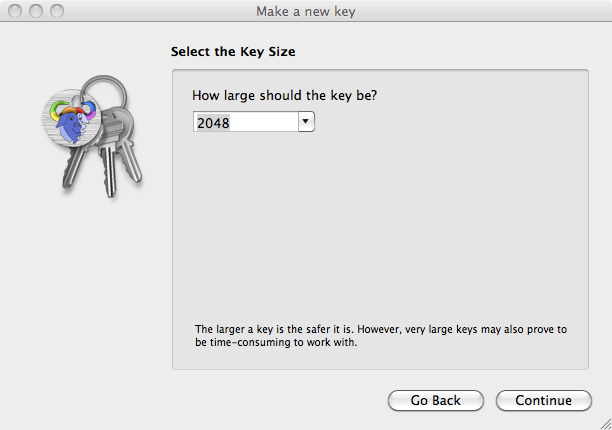
ELG-E keys may be between 1024 and 4096 bits long.
What keysize do you want? (2048)
Requested keysize is 2048 bits
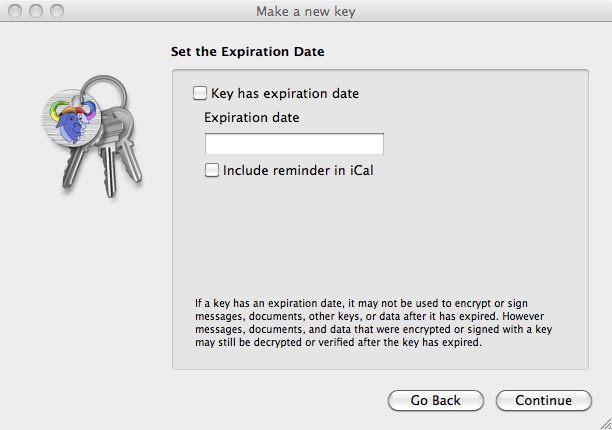
Please specify how long the key should be valid.
0 = key does not expire
<n> = key expires in n days
<n>w = key expires in n weeks
<n>m = key expires in n months
<n>y = key expires in n years
Key is valid for? (0)
Key does not expire at all
Is this correct? (y/N) y
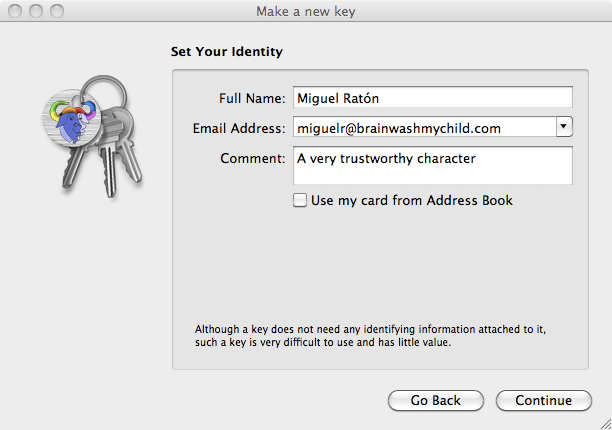
You need a user ID to identify your key; the software constructs the user ID
from the Real Name, Comment and Email Address in this form:
"Heinrich Heine (Der Dichter) <heinrichh@duesseldorf.de>"
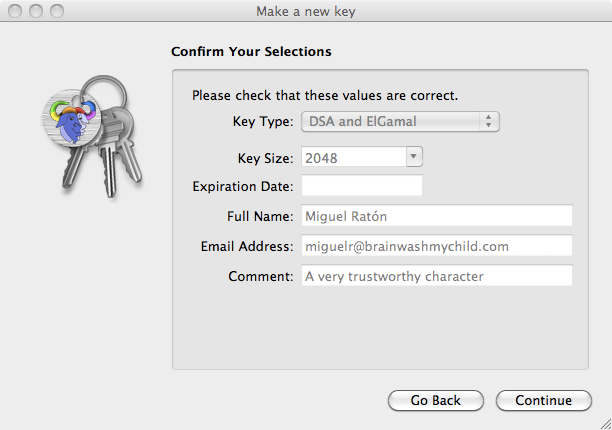
Real name: Miguel Ratón
Email address: miguelr@brainwashmychild.com
Comment:
You are using the `utf-8' character set.
You selected this USER-ID:
"Miguel Ratón <miguelr@brainwashmychild.com>"
Change (N)ame, (C)omment, (E)mail or (O)kay/(Q)uit? O
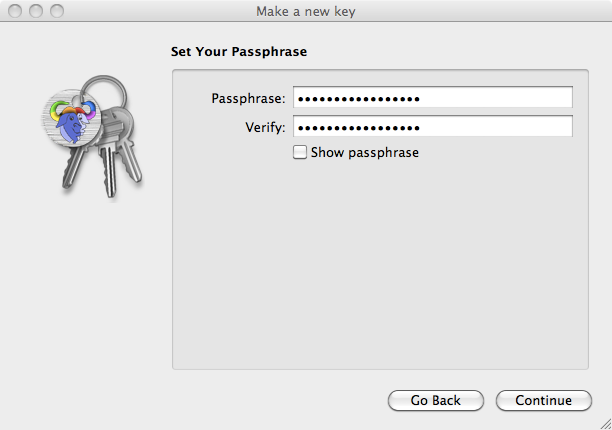
You need a Passphrase to protect your secret key.
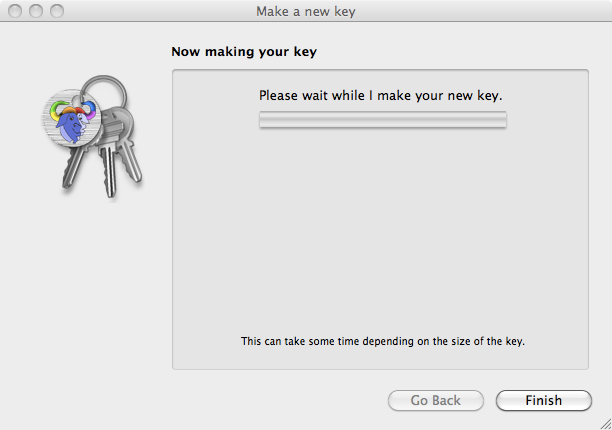
We need to generate a lot of random bytes. It is a good idea to perform
some other action (type on the keyboard, move the mouse, utilize the
disks) during the prime generation; this gives the random number
generator a better chance to gain enough entropy.
++++++++++++++++++++++++++++++++++++++++++++++++++.+++++++++++++++..++++++++++.++++++++++++++++++++++++++++++++++++++++++++++++++...+++++>++++++++++..>..+++++......<+++++.........................................................+++++
We need to generate a lot of random bytes. It is a good idea to perform
some other action (type on the keyboard, move the mouse, utilize the
disks) during the prime generation; this gives the random number
generator a better chance to gain enough entropy.
.++++++++++++++++++++..+++++.+++++++++++++++..+++++.+++++++++++++++++++++++++.++++++++++.+++++++++++++++++++++++++.+++++++++++++++.++++++++++...++++++++++.+++++>++++++++++>+++++>+++++.................................<+++++
gpg: key C723F1BA marked as ultimately trusted
public and secret key created and signed.
gpg: checking the trustdb
gpg: 3 marginal(s) needed, 1 complete(s) needed, classic trust model
gpg: depth: 0 valid: 8 signed: 0 trust: 0-, 0q, 0n, 0m, 0f, 8u
gpg: next trustdb check due at 2011-06-13
pub 1024D/C723F1BA 2010-03-05
Key fingerprint = E96E F793 54AF CDCE 1103 F66E BEF1 9B22 C723 F1BA
uid Miguel Ratón <miguelr@brainwashmychild.com>
sub 2048g/16C4D6032 2010-03-05
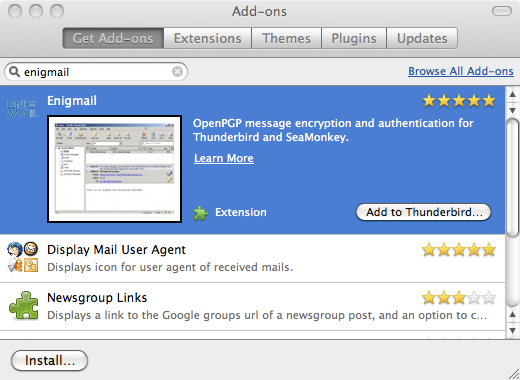
Using GnuPG with Thunderbird
GnuPG integrates splendidly with the Thunderbird email client using an add-on called [Enigmail|http://enigmail.mozdev.org/home/index.php]. if you already have Thunderbird set-up and installed, the easiest way to install Enigmail is via Thunderbird itself. Choose Add-ons from the Tools menu, which will take you to the Add-ons window. Choose the Get Add-ons tab and in the Search All Add-ons field on the top left, enter Enigmail and hit the enter key. You should see Enigmail returned as one of the results, like the following:
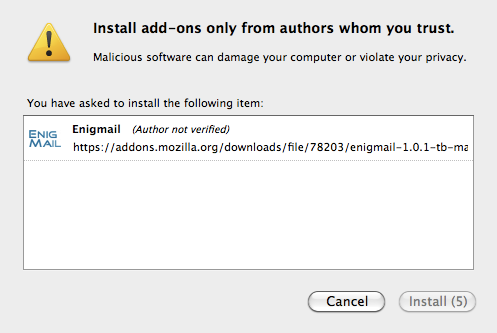
Click the Add to Thunderbird to the right of the Enigmail entry, you'll get the following window to confirm you wish to install Enigmail. When the button to the right says Install Now click it and Enigmail will be installed.
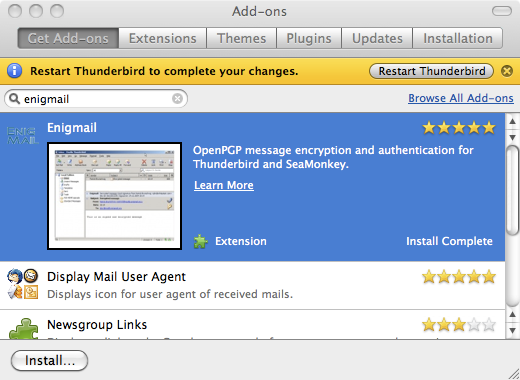
Once installed you'll be prompted to restart Thunderbird, go ahead and do it:
(In the above instructions, if you have a problem searching for Enigmail, try downloading it from the web and installing it manually https://addons.mozilla.org/en-US/thunderbird/search?q=Enigmail.)
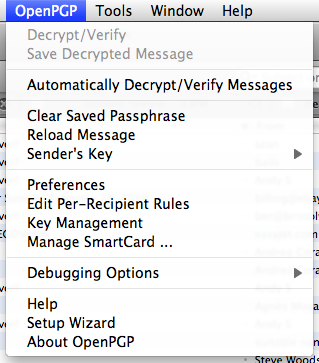
Now it's installed and Thunderbird's restarted, you'll spot a brand-new menu OpenGPG:
- OpenGPG set-up wizard needs to go here***
We're ready to start encrypting and decrypting our emails using Thunderbird.
Sending and encrypting an email
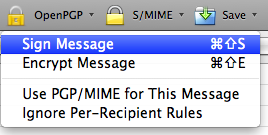
When you go to create a new message, you'll now spot a new icon available to you:
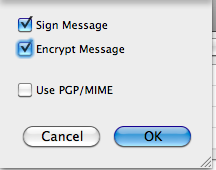
Using this new menu you can choose whether you want to encrypt and/or sign your email message.
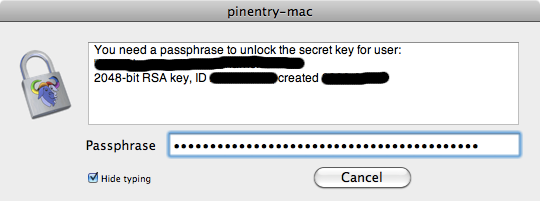
When you click send, if you've chosen to sign the message, then you'll be prompted for the passphrase that you entered when you created your PGP key.